An Approved Scanning Vendor (ASV) is a company approved by the Payment Card Industry Security Standards Council (PCI SSC) that offers a scan solution to validate a merchant or service provider’s (scan customer) compliance with PCI DSS Requirement 11.2.2.
An ASV’s scan solution is the set of security services and tools used to scan a scan customer’s external environment. The requirements (11.2.2 or 11.3.2 in version 4.0) mandate that scan customers complete quarterly scans of their external network using an ASV.
The scans are designed to test for vulnerabilities from the outside in, looking for any potential and well-known weaknesses a bad actor can exploit to gain access to the company’s cardholder data environment (CDE). The overall purpose of ASV scanning is to identify low-hanging fruit that hackers can find on the internet using scanning tools or targeting your environment directly.
If you’re looking for a new approved scanning vendor, looking to switch to a new one, or want to negotiate a better contract with your current PCI consultants, this article will help you understand ASVs, what they offer, how they differ, and what if anything you can adjust in the scanning process.
- Find the Right PCI ASV Fast
- Key Takeaway: Listed ASV vs PCI Consultants
- What's the PCI ASV Requirement?
- What Exactly Must Be Scanned?
- How Approved Scanning Vendors Work
- What's The Difference Between Approved Scanning Vendors?
- How Much Do PCI ASVs Charge?
- Real-World ASV Case Studies With Costings
- How To Choose a PCI ASV?
- How Do You Fail an ASV Scan?
- What's an Incomplete ASV Scan?
- What's a Remediation Scan?
(NOTE: If you’re looking for an Approved Scanning Vendor, our free tool below matches your firm with a top-rated PCI ASV that can meet your needs and budget.)
Key Takeaway: Listed ASV vs PCI Consultants
There are two major ways that PCI-compliant companies manage their ASV scans.
- The first is to contract a listed PCI ASV company (the ones that are listed by the PCI council) to run the scan and generate the reports for you. However, it is critical to understand that some of the listed PCI AS vendors are not “vendors” as such but software solutions (Qualys is an example) that anyone with experience can run either from inside or outside your company.
- The second way is to use a PCI consultant who uses one of these ASV software solutions to perform your vulnerability scans for you.
What’s the difference between these two options?
First, there is no general difference regarding compliance requirements. Both options, provided they are performed correctly, will help you meet the PCI compliance requirement. The difference is in the availability and the cost.
There are only (at the time of writing) 75 listed PCI ASV solutions, and they cater to the entire world’s PCI requirements. This can make the listed solutions less available, and, because they are so exclusive, more expensive.
By contrast, there are hundreds of registered PCI consultants who can manage your ASV scans effectively using one of the listed, cloud-based ASV solutions. These consultants are often (but not always) cheaper, more available, and can be more helpful in providing remediation when vulnerabilities arise, guidance on scoping questions, and more. In our work matchmaking companies with PCI solutions, this option is almost always a better fit for small to medium businesses.
What’s the PCI ASV Requirement?
A company that accepts, processes, or stores credit card information must assess the security of its internet-facing systems according to PCI DSS, and there are several requirements to be met in so doing:
- Maintain compliance with PCI DSS 11.2.2, or 11.3.2 in version 4.0, at all times
- Use an ASV from the list of approved vendors from the PCI SSC website;
- Define the scope of external vulnerability scanning (e.g., IP addresses and domains for all internet-facing systems), providing a complete, current, accurate inventory to the ASV. This needs to include all externally facing IP addresses and domains in the network that can access a PCI environment. Even if you have a DMZ or other protections in place, they do not eliminate the need for ASV scanning or a reason to exclude them from the scope. If it’s external and can provide a pathway from the outside into a PCI environment, regardless of other security protections, it should be in your scope;
- Configure active IPS/IDS so they do not interfere with the ASV’s scan. This means that you need to whitelist your ASV scanner’s IP addresses in your environment. The point of ASV scanning isn’t to make sure your security appliances are working correctly. The point it to identify any potential vulnerabilities. Just because an IPS/IDS might block them doesn’t mean they aren’t there. If the ASV scanners detect security appliance interference, it will fail your scan. You will not be able to receive a passing scan as long as interference is detected by the scanning platform. This check is a required part of the PCI requirements for ASV scanning companies to build into their platforms;
- Coordinate with any hosting or cloud service providers to allow ASV scans. Review the contracts with your hosting infrastructure companies to ensure that they allow you to either scan your environment directly without any notification, or if there is a defined process to request scanning. By scanning without prior approval, you could potentially breach your contracts with that company and disrupt your own service or the service of other customers. Remember, ASV scans are a vulnerability scan like any other. So these scanners can generate a lot of traffic and they can inadvertently cause a denial of service scenario, which is why these companies require prior notification of scans.
- Provide a rationale for excluding any network components from the scope. For any external IPs or domains you deem out of scope, you need to justify why they are out of scope. This explanation will ultimately be deemed as “valid” or not by your QSA, ISA, or whoever is performing your PCI assessment. Valid reasoning for excluding a network could be that it’s a completely separate network that doesn’t touch a PCI-scoped network at all and cannot affect the security of the PCI-scoped network, for example;
- Scan frequently. You must scan at least once a quarter, per PCI DSS requirements. Since there can be vulnerabilities that need to be addressed, do not wait to the last minute when your scan is due as this could cause you to be un-compliant. Instead, scan at the beginning of each quarter and throughout the quarter to get ahead of vulnerabilities. Doing this will give you and your organization enough time to properly address them. Depending on the vulnerability and your environment, fixes can take some time;
- Provide reasoning or evidence to the ASV company to resolve any disputed findings (e.g., suspected false positives). False positives are a plenty in ASV scanning. Remember, scanning is automated. If the scanner cannot determine what’s going on, it will make the best recommendation. A common one is HTTP issues or encryption discovered. A reasoning could be that since this is in a DMZ, and behind a firewall and load balancer, the internal servers have self-signed certs or no HTTPS enabled. Encryption is terminated by the load balancers to the servers. All traffic is served to the internet through encryption and proper HTTP security headers by either the load balancers or firewalls. Since the scanner needed to bypass these security appliances, it didn’t know that those protections were in place;
- Review ASV’s scan report and correct any identified vulnerabilities that cause a scan to be non-compliant. For any valid vulnerabilities, fix them immediately and rescan until you get a passing scan. Sometimes this takes multiple tries;
- Provide any compensating controls for a component not included in the scope (e.g., router “A” configuration must remain due to reason X or Y, but the company ensures its security through a particular network monitoring exceptions tool);
- Provide the completed ASV scan report to your acquirer(s) and Participating Payment Brand(s) where required. Additionally, keep your quarterly passing scans handy for your annual PCI assessment. You must provide these passing quarterly scans to your QSA, ISA, or whoever is performing your PCI assessment;
What Exactly Must Be Scanned?
The scan customer is responsible for ensuring the components that make up the external network of the CDE are scoped in and provided to the Approved Scanning Vendor and include:
- Internet protocol (IP) addresses (for all the customer’s locations if multiple);
- Servers (Database, web, application, mail, DNS, proxy);
- Firewall and routers;
- Operating systems;
- Built-in user accounts;
- Common services;
- SSL/TLS;
- Virtualization components; and
- Wireless access points.
The customer must include any external network component “touching” cardholder data, or that can connect to any PCI-scoped networks.
Note: Smaller companies often have “flat networks,” meaning every component has access to every other component on the network. In this case, the ASV scans the entire network. To help ensure proper scoping, the customer should consult with a security professional, such as PCI DSS Qualified Security Assessors (QSAs). (Note: You can compare PCI QSA companies at our vendor directory)
As a best practice with cybersecurity, you should at least have a DMZ, or demilitarized zone, that acts as a buffer between your internal network and the Internet. This adds another barrier between your internal networks and potential hackers by keeping public-facing servers and equipment separated from internal equipment. In the event equipment is breached in the DMZ, the rest of your network isn’t completely at risk.
Additionally, to further reduce your PCI DSS scope, consider creating a PCI Zone through segmentation. Segmentation isn’t a PCI DSS requirement; however, it allows you to descope the rest of your environment that doesn’t touch PCI.
This can greatly reduce the size of your assessment and the effort needed to assess each year. It will also better protect your PCI network and make it easier to manage since everything is in one area that can be better protected with more security. Similarly to the DMZ, if a device on the internal network, like an employee workstation, is compromised, your PCI environment isn’t completely at risk and is better protected.
How Approved Scanning Vendors Work

The customer engages with an ASV from the ASV listing approved by PCI Security Standards Council. The ASV scans the customer’s external network structure (e.g., IP addresses, domains) to identify any weaknesses that an attacker can exploit from the internet.
- The customer provides scan scope to the PCI ASV (i.e., a list of IP addresses, domains, routers, etc.); ensures coverage of all external-facing components that make up the CDE;
- The ASV runs scans that are if-then scenarios on the external system components listed in the scope to identify system settings in which a vulnerability exists that can be exploited;
- The ASV provides scan results to the customer;
- The customer reviews the scan results and, in the event of identified vulnerabilities, performs root cause analysis and remediates the vulnerability;
- The customer engages the ASV to rescan those components with vulnerabilities. This cycle continues until all rescans return a clean results report;
- The ASV provides the original scan results report, the rescan(s) reports, and supporting documentation to the customer;
- The customer provides reports and documentation to their acquiring bank and PCI assessor for annual PCI assessments;
(NOTE: Use our free matching tool to quickly connect with top-rated PCI ASVs that suit your company’s needs and budget.)
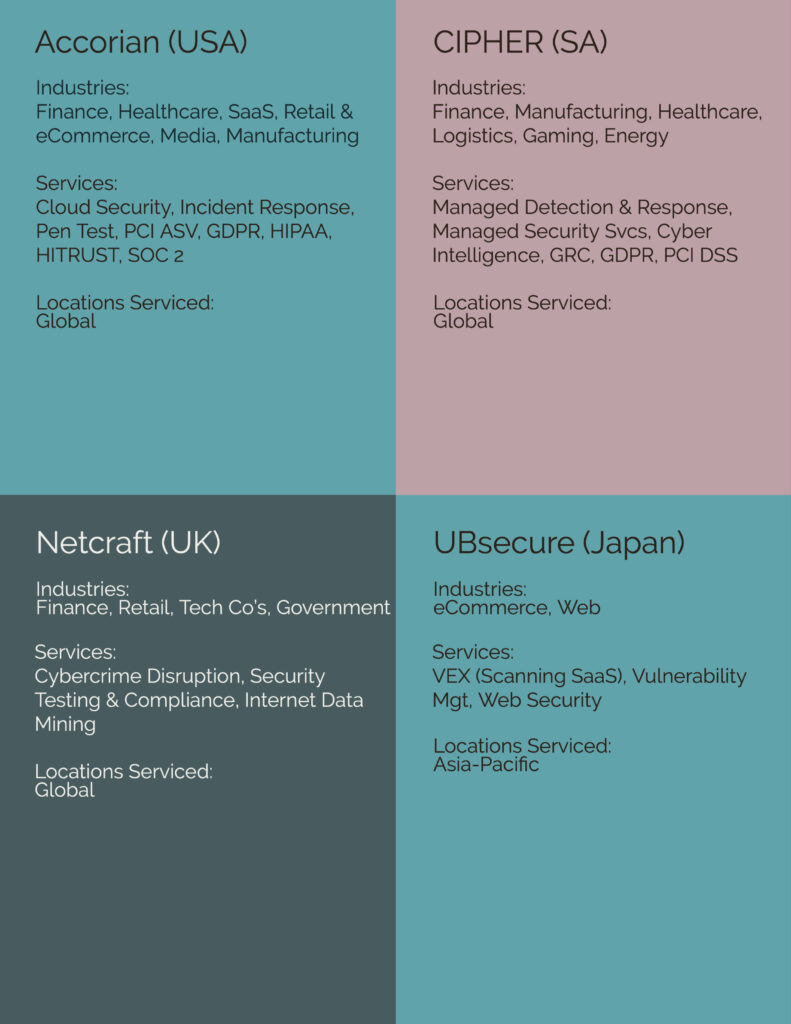
What’s The Difference Between Approved Scanning Vendors?
There are currently 75 ASVs listed on the PCI SSC site. Several are “In Remediation’ meaning they have violated part of the Approved Scanning Vendor Program and actively working to remediate.
The differences between ASVs are numerous. ASVs operate out of different countries, serving various industries, offering multiple services, and serving varied geographical areas. The following depicts the diversity of ASVs on the PCI SSC site:
How Much Do PCI ASVs Charge?
ASV charges are as varied as the types of ASVs. A large customer can engage with an ASV to provide multiple services, including ASV scanning, at no additional cost.
Company A is a healthcare chain with offices across the USA. It can secure an ASV who provides best practice services to healthcare organizations. In addition to PCI, Company A can obtain HIPAA consultancy and compliance testing, as well as HITRUST.
Company B is a website offering children’s toys. It has one office in London and ships to customers worldwide. It can engage with an ASV specializing in eCommerce and website security, which will provide IP scanning at a set cost per IP address per year.
The range for this is from $100 to $200 per IP address. The price may be per IP address, as are the pricing structures. Some ASVs charge an annual fee as low as $70 for PCI Scanning Services if the scan customer purchases other services in combination.
At the other end of the spectrum are ASNs who charge per IP address, quarterly or annually, and those prices range from $100 to $200 per IP address.
Real-World ASV Case Studies With Costings
In this section, we’ve presented some real-world examples of PCI ASV contracts in different organizations to help those new to ASV scans understand possible deal structures and different means of getting compliant scans done.
Case Study #1: Sweetheart Fintech Deal
A business-to-business financial technology company was able to attain a sweetheart deal for their ASV scanning. Essentially, this organization was able to attain vulnerability scanning from a certified ASV vendor for free as part of their contract to perform penetration testing and PCI certification within their environment. While not all companies can gain this, it is not uncommon to see organizations able to bundle multiple PCI services together and achieve a vulnerability assessment that meets requirement 11.2.
Industry: FinTech
Size of the Organization: <1000
Scope: External: Less than 10 IP addresses and applications, Internal: less than 15 IP addresses
Cost: No cost associated with the assessments
Notes: Due to the size and complexity of the cardholder data environment, the free assessments were likely attained. The total effort for the ASV to run and generate a report for this organization was nominal. As part of the negotiation, the vendor most likely added this free service to add additional value to the contract.
Case Study #2: Leveraging Existing Technology
When it comes to meeting requirement 11.2 for PCI DSS, the only requirement is that the vendor or solution be certified as an Approved Scanning Vendor. This opens the doors for consultancies, vendors, and hybrid solutions to meet the PCI requirement for an organization.
Most organizations have a relationship with an existing vendor or consultancy that may allow them to meet this requirement. In this case study, a financial service provider in the consumer space leveraged the capability of a vendor that was already contracted for vulnerability management across the organization. Since the vendor was an ASV and offered the service under the existing contract, the organization was able to leverage existing tools and scanners and increase the operational efficiency of its security program.
By implementing a unique report for only the assets in scope for PCI, the organization was able to leverage the scanning and assessment work that was underway for the full organization without reporting it all to their QSA.
Industry: Financial Services
Size of the Organization: >1500
Scope: External: ~50IP addresses and applications, Internal: ~30 IP addresses and systems
Cost: ~$60,000 for a full enterprise vulnerability management solution per year.
Notes: In this case study, it is not possible to separate the cost of the PCI ASV assessments from the greater vulnerability management program because the organization was leveraging the enterprise vendor. This is a valid approach to meet this requirement and requires little to no additional effort to contract with a consultancy to perform the assessment. In both cases, the in-scope IP addresses must be identified before the assessment starts.
The only difference for this organization is that the security staff was required to configure the report generation within the tool and the frequency of reporting. Once this was set, it was automatically completed and emailed to all stakeholders with no additional maintenance needed.
How To Choose a PCI ASV?
The PCI SSC has performed much of the heavy lifting in selecting ASVs for the customer, providing a list of vendors approved by the PCI SSC, but it’s worth considering other criteria when reviewing ASVs.
If you’re not using our free matching service to quickly connect with top-rated ASVs that can meet your needs and budget, here are 5 considerations to make as part of your due diligence.
Customer Industry
Is the customer operating in one or multiple industries? A manufacturing company may also have a branch for energy services. The brick-and-mortar retail store may also have eCommerce lines of business.
Transaction Volume
How many credit card transactions does the customer process annually (and what is the PCI compliance level necessary)? A customer with a high transaction volume may find an ASV whose focus is PCI DSS the best fit.
Geography
The customer’s base location, be it local, country-wide, or global, can drive them to align with an ASV whose services are of similar geographic operations.
Self-Service
A big help if you want to be more hands-on is to have a self-service ASV. This means that your organization can log in directly to the platform and manage your own scans. This reduces the time spent communicating back and forth between your organization and the ASV. By being able to start your own scans, you can rescan immediately after fixes have been implemented and check to see if they worked. On the other hand, if you wish to have this fully outsourced, this consideration might not be for you.
Service Offerings
Some ASVs, for example, provide other services and functionality apart from solely ASV scanning. If an organization already contracts with an ASV for internal vulnerability scanning, it will be simpler to use them from an internal vendor management stance. Additionally, if you are looking to add other services from the vendor at a later time, you can have everything all in one place instead of using different platforms to keep things simple.
Other Considerations
A customer should understand their cybersecurity maturity posture (e.g., the customer performs regular vulnerability scanning, has antivirus software, and mature change management processes) should be considered. Company size, maturity, and regulatory needs should drive alignment with the ASV selected to perform scanning services to meet PCI DSS 11.2.2. For example, a company with a fully staffed security team may not need one of the larger ASVs.
NOTE: See our list of specialist PCI compliance vendors here.
How Do You Fail an ASV Scan?
Failed ASV scans can happen for several reasons, like misconfigured ports, outdated antivirus software, outdated security patches, and one-off anomalies. There are a few commonly seen reasons for a failed vulnerability scan, and the customer should proactively review these configurations and update them as needed before the ASV scan:
- TLS Version 1.0, 2.0, or 3.0 protocol(s) is (are) not disabled (can allow an outside actor access the CDE) – review before the PCI ASV scan and make sure all are disabled; and
- SSL Certificate with Wrong Hostname—To avoid this, make sure the port names match those on the SSL Certificate, which is current and signed by a Certificate Authority (CA).
- False positives – As we mentioned earlier, sometimes you fail a scan just because the scanning appliance doesn’t see what’s actually there due to one reason or another. As long as you can justify the false positive, you can submit it to the ASV, and if approved, you can pass that finding.
What’s an Incomplete ASV Scan?
An incomplete ASV scan may occur due to the company’s internal security systems (e.g., IDS, IPS) not being configured to allow the ASV external scan. The customer’s internet provider may block the vulnerability scan as it detects suspicious activity.
The customer should request the ASV provide the necessary information to be communicated to the ISP, hosting providers, or cloud service providers before scans. By working closely and collaboratively with the ASV, the customer can, ahead of time, ensure proper configurations both onsite and with the ISP to prevent a vulnerability scan from completing.
What’s a Remediation Scan?
When an ASV scan fails, the results are directly communicated to the customer by the ASV. The scan customer must perform a root cause and impact analysis, identify a remediation plan, and implement the remediation following formal change management processes.
The customer should immediately segment the network section, device, WAP, etc., where the vulnerability exists. After remediating the exposure, the customer notifies the ASV to perform a rescan of the failed components.
The customer has 90 days to remediate identified vulnerabilities and perform a rescan of their external network by the ASV. As a best practice, the customer should maintain all documentation capturing root cause, impact, remediation, and retesting per the scan customer’s evidence retention policy.